The Cyberattack on Nobitex: A Strategic Strike in the Israel-Iran Digital Conflict
I. Executive Summary
On June 18, 2025, Nobitex, Iran's largest cryptocurrency exchange, became the target of a significant cyberattack claimed by "Gonjeshke Darande," also known as "Predatory Sparrow," a hacking group widely associated with Israel. The incident resulted in a reported loss exceeding $48 million in Tether (USDT) from Nobitex's hot wallets. Following the breach, Gonjeshke Darande issued a public warning, threatening to release Nobitex's source code and internal network information within 24 hours, cautioning that any remaining assets on the platform would be at risk.
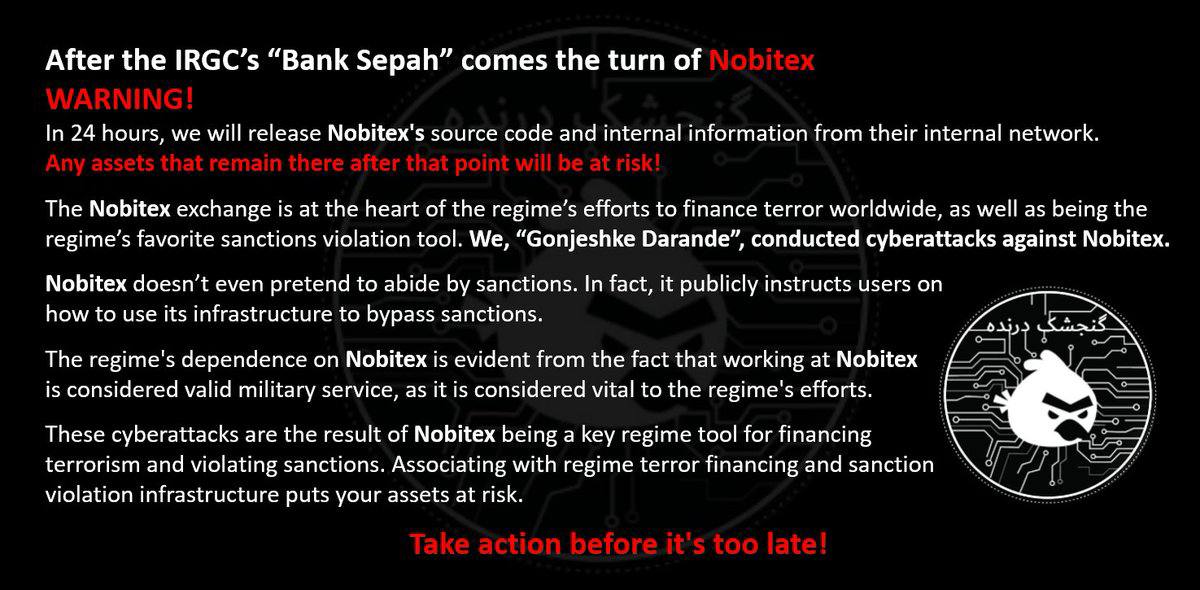
This cyberattack follows a pattern of sophisticated operations by Gonjeshke Darande against Iranian critical infrastructure, including a claimed hack on Iran's state-owned Bank Sepah just one day prior, on June 17, 2025. The group explicitly accused Nobitex of being a central instrument for the Iranian regime in financing global terrorism and serving as its primary tool for circumventing international sanctions. These accusations are underscored by claims that Nobitex not only disregards sanctions but actively provides public instructions to its users on how to bypass them, and that employment at the exchange is considered equivalent to military service under Iranian law. The attack on Nobitex represents a critical escalation within the ongoing cyber conflict between Israel and Iran, highlighting the increasing strategic importance of financial institutions and cryptocurrency platforms as targets in modern geopolitical warfare.
II. Introduction: The Escalating Cyber Front
The relationship between Israel and Iran has long been characterized by an undeclared, yet persistent, cyber conflict. This digital confrontation involves a series of tit-for-tat attacks that frequently target critical infrastructure, state-affiliated entities, and financial systems in both nations. Cyber operations have emerged as an indispensable component of both countries' geopolitical strategies, enabling asymmetric warfare and providing a degree of plausible deniability for actions that might otherwise provoke a more overt military response.
A notable development in this cyber warfare is a discernible shift in the nature of targets and objectives. Historically, cyberattacks often focused on physical infrastructure, aiming for disruption or sabotage, as exemplified by incidents like Stuxnet or attacks on gas stations and steel mills. However, the recent emphasis on financial institutions, such as Bank Sepah, and particularly cryptocurrency exchanges like Nobitex, signals a strategic evolution. This change indicates a move beyond mere operational disruption to directly impacting an adversary's economic stability and illicit financial flows, which are crucial for sustaining state-sponsored activities and proxy networks. By targeting financial conduits like Nobitex, the objective is to cripple the Iranian regime's capacity to circumvent sanctions and fund its operations, thereby exerting economic pressure through digital means. This represents a direct assault on the financial arteries of the state.
The Nobitex cyberattack stands as a high-profile manifestation of this escalating conflict. The public warning issued by Gonjeshke Darande, prominently displayed in the user query's image, underscores the audacity and strategic intent behind the operation. The targeting of a cryptocurrency exchange carries particular significance given the growing role of digital assets in illicit finance and sanctions evasion, especially for heavily sanctioned regimes like Iran. Cryptocurrencies offer inherent advantages such as ease of transactions, increased speed, anonymity, and a relative lack of regulation, making them a potent tool for circumventing traditional financial sanctions. This dual nature—being a legitimate financial innovation while simultaneously serving as a conduit for illicit activities—transforms crypto exchanges into strategic targets in cyber warfare. The Nobitex attack underscores that cryptocurrency platforms are no longer simply financial services but have become integral components of critical infrastructure in geopolitical conflicts. States are now actively engaging in offensive cyber operations against these platforms to disrupt an adversary's financial lifeline, acknowledging cryptocurrency's pivotal role in bypassing conventional financial controls. This evolving landscape suggests a pressing need for international frameworks to address cyberattacks on crypto infrastructure, even when such infrastructure is linked to illicit activities.
III. The Nobitex Cyberattack: A Detailed Account
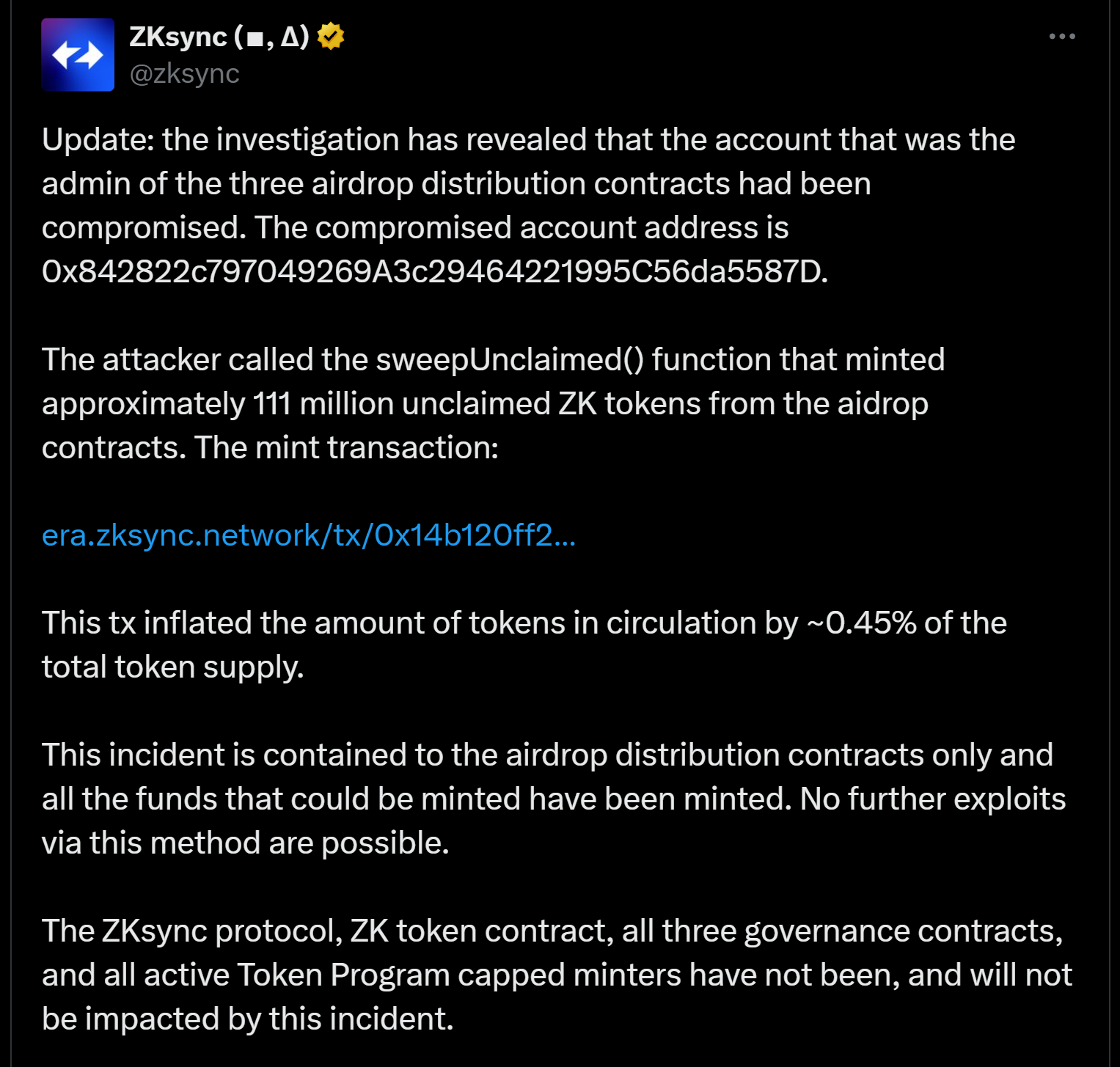
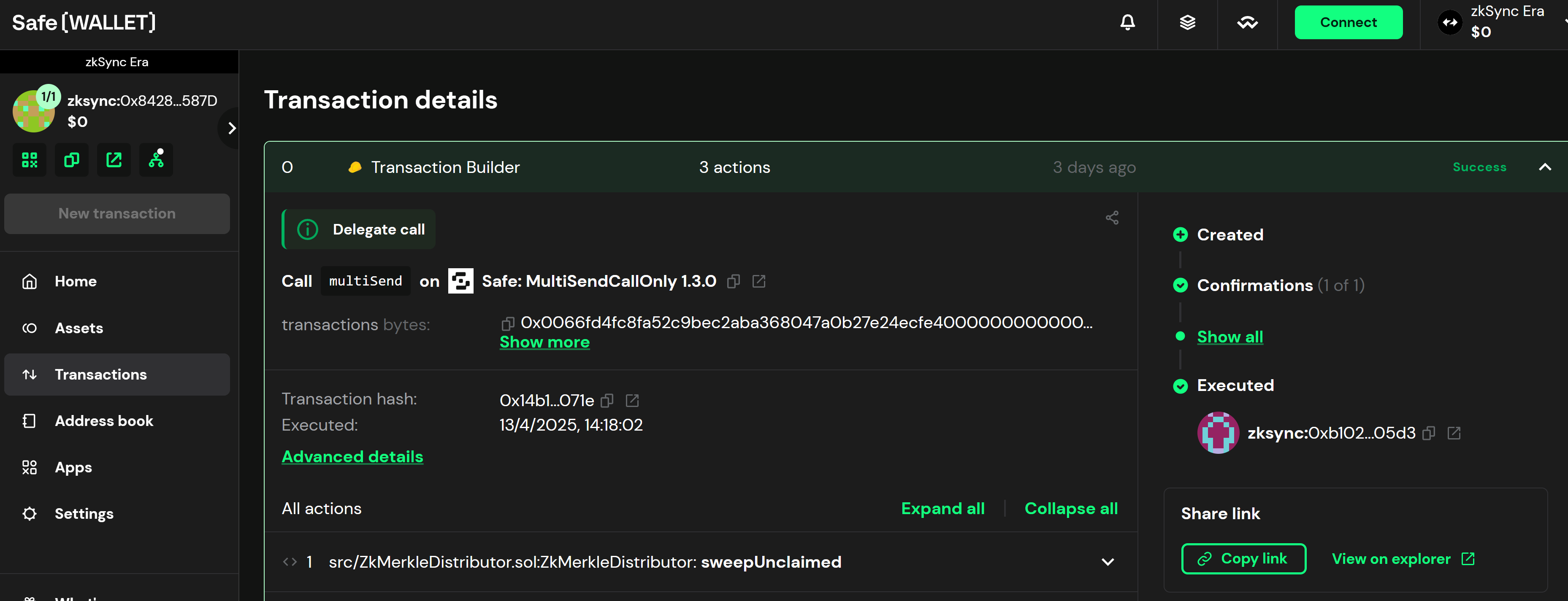
The cyberattack on Nobitex unfolded on June 18, 2025, just one day after Gonjeshke Darande claimed responsibility for a separate, impactful hack on Iran's state-owned Bank Sepah. In a public declaration, the hacking group, Gonjeshke Darande, asserted its responsibility for the Nobitex breach. The group issued a stark warning: it intended to release Nobitex's source code and internal network information within 24 hours, explicitly cautioning that "any assets that remain there after that point will be at risk!". The group's public statements were unequivocal, accusing Nobitex of being "at the heart of the regime's efforts to finance terror worldwide, as well as being the regime's favorite sanctions violation tool".
These public warnings and explicit accusations, including the 24-hour ultimatum, extend beyond mere technical disruption. They are meticulously designed to induce panic among Nobitex users and to sow widespread distrust in Iranian financial institutions. Such actions aim to undermine public confidence in the Iranian regime's financial infrastructure and its capacity to safeguard its citizens' assets, potentially triggering capital flight and internal unrest. This amplifies the impact of the cyberattack far beyond the immediate technical breach, leveraging information operations as a potent form of psychological warfare.
Nobitex promptly confirmed the incident, acknowledging a "major security breach" and "unauthorized access to a portion of our reporting infrastructure and hot wallet" on June 18, 2025. The exchange reported a significant financial loss, specifically over $48 million in Tether (USDT) via the Tron network. Despite the breach, Nobitex sought to reassure its users that funds held in cold wallets remained secure and pledged full compensation for all damages through its insurance fund and company resources. As a precautionary and investigative measure, the platform's website and mobile application were taken offline.
The fact that the $48 million loss specifically targeted Nobitex's hot wallets highlights a critical vulnerability point for cryptocurrency exchanges. While cold wallets are generally considered more secure for long-term storage, hot wallets are essential for maintaining liquidity and facilitating daily operational transactions. This incident demonstrates that even large exchanges can be susceptible to sophisticated attacks targeting their operational funds, despite assurances regarding the safety of user funds in cold storage. It underscores the inherent tension between operational accessibility and robust security, compelling exchanges to meticulously balance liquidity requirements with the imperative to protect assets from state-sponsored or highly skilled threat actors.
Gonjeshke Darande's threat to release Nobitex's source code and internal information represents a significant escalation. The release of source code could expose underlying vulnerabilities in the exchange's platform, potentially enabling further exploitation. More critically, the disclosure of internal data could reveal sensitive information, including user identities, transaction patterns, and, most importantly, the specific methods Nobitex employs to bypass international sanctions. This information could be profoundly damaging to Nobitex and its users, while simultaneously proving invaluable to international sanctions enforcement bodies. This threat is not merely about technical exposure; it is a strategic maneuver to leverage transparency against an entity accused of illicit activities. By exposing Nobitex's operational methodology, including how it "publicly instructs users on how to use its infrastructure to bypass sanctions" 1, Gonjeshke Darande aims to provide actionable intelligence to international regulators, such as the Office of Foreign Assets Control (OFAC) and the Financial Action Task Force (FATF), and law enforcement agencies. Such disclosures could lead to more effective targeting of Nobitex's network, its users, and its facilitators, thereby tightening the constraints on Iran's sanctions evasion efforts and potentially deterring others from engaging in similar activities.
IV. Gonjeshke Darande: The "Predatory Sparrow"
The hacking group, known as "Predatory Sparrow" in English and "Gonjeshke Darande" in Persian, has emerged as a prominent actor in the cyber landscape targeting Iran. While Israel maintains a consistent policy of ambiguity regarding its cyber operations and has never officially acknowledged any association with the group, Gonjeshke Darande is widely believed to be linked to Israeli military intelligence, with some speculation pointing to Unit 8200. The group's operations consistently demonstrate "real skill and sophistication" 7 and possess "technical proficiency beyond that of a typical hacktivist group" 11, strongly suggesting access to state-level resources, training, and operational planning. The strategic utility of this "plausible deniability" in cyber warfare is significant. It allows Israel to achieve strategic objectives, such as disrupting Iranian infrastructure and imposing economic costs, without direct attribution. This approach helps manage escalation risks, enabling aggressive cyber action against an adversary without necessarily crossing a threshold that might necessitate a conventional military response. This model of state-sponsored, deniable cyber operations is a growing trend in international conflict, complicating diplomatic and legal responses.
Gonjeshke Darande has a track record of high-profile cyber operations against critical Iranian infrastructure:
- Bank Sepah (June 17, 2025): The group claimed responsibility for destroying data at Iran's state-owned Bank Sepah, accusing it of funding Iran's military. Reports indicated the bank's website was offline, and customers experienced issues accessing their accounts. This attack immediately preceded the Nobitex incident.
- Gas Stations (October 2021, December 2023): Gonjeshke Darande paralyzed gas stations across Iran, affecting up to 70% of the country's stations. The group stated these attacks were a response to Iranian aggression and warned of further actions. They claimed to have gained access to payment and management systems.
- Steel Factory (2022): The group claimed responsibility for a cyberattack that forced the Iranian state-owned Khuzestan Steel Co. to halt production.
- Railway System: Gonjeshke Darande has also claimed attacks on Iran's rail system network.
This consistent targeting strategy against Iran's critical economic and societal infrastructure (banks, gas stations, steel, railways) indicates a deliberate effort to inflict economic pain and generate public dissatisfaction within Iran. The motivations articulated by the group often link these targets directly to the Iranian regime's illicit activities or aggressive posture. By disrupting essential services and financial infrastructure, the group aims to create internal pressure on the regime, highlighting its vulnerabilities and potentially eroding its legitimacy. This approach extends beyond traditional cyber espionage or sabotage, entering the realm of sustained economic warfare conducted through digital means.
The stated motivations for Gonjeshke Darande's attacks are consistently articulated as responses to the "aggression of the Islamic Republic and its proxies" 9, and they specifically target entities involved in "financing terror worldwide" and "sanctions violation". For the Bank Sepah attack, the group cited the bank's alleged role in funding Iran's military, including its ballistic missile and nuclear programs. This consistent articulation of clear justifications for its attacks, framing them as responses to Iranian illicit activities, serves as a narrative weapon. By publicly stating these motivations, the group aims to legitimize its actions on the international stage and potentially garner support or at least tacit acceptance from nations concerned about Iran's behavior. This narrative also serves to demoralize the target (the Iranian regime) and potentially encourage internal dissent by framing the attacks as direct consequences of the regime's own actions, rather than unprovoked aggression. It is a strategic use of public messaging as an integral part of the overall cyber operation.
Despite the disruptive nature of their operations, Gonjeshke Darande has publicly claimed a degree of "ethical restraint." The group asserts that its operations are "conducted in a controlled manner while taking measures to limit potential damage to emergency services," and that they "delivered warnings to emergency services across the country before the operation began". They also claimed to have intentionally left a portion of gas stations unharmed, despite possessing the capability for full disruption. Similarly, for the steel factory attack, they claimed to have chosen an early morning time (5:15 am) to minimize risks and stated they could have caused more severe damage but refrained for "ethical reasons". his claim of ethical restraint, while seemingly paradoxical given the targeting of critical civilian infrastructure, is likely a strategic communication tactic. It attempts to portray the group as a responsible actor, differentiate themselves from indiscriminate attacks, and potentially avoid international condemnation for excessive harm to civilians. It may also be an attempt to subtly establish a precedent for "rules of engagement" in cyber warfare, even if self-imposed. This highlights the complex moral and strategic considerations in modern cyber conflict, where even state-linked actors attempt to shape perceptions of their conduct.
Table 1: Key Cyberattacks by Gonjeshke Darande (Predatory Sparrow)
| Date | Target | Type of Infrastructure | Stated Motivation | Reported Impact |
|---|---|---|---|---|
| June 18, 2025 | Nobitex | Cryptocurrency Exchange | Financing terror, sanctions violation tool, military service link | \~$48M USDT loss, threat to release source code/internal data, website/app offline 1 |
| June 17, 2025 | Bank Sepah | State-owned Bank | Funding Iran's military, ballistic missile, and nuclear programs, circumventing international sanctions | Data destruction claimed, website offline, customer access problems, broader financial disruption 1 |
| December 2023 | Gas Stations | Fuel Distribution System | Response to Iranian aggression and proxies | Paralyzed \~70% of Iran's gas stations 9 |
| October 2021 | Gas Stations | Fuel Distribution System | Disrupting the regime, maximizing public dissatisfaction | Paralyzed gas stations across the country 9 |
| 2022 | Khuzestan Steel Co. | State-owned Steel Factory | Companies flouting international sanctions | Forced production halt 9 |
| Various | Railway System | Transportation Network | Not explicitly stated for specific attacks, part of general disruption | Attacks claimed 7 |
V. Nobitex: A Nexus for Sanctions Evasion and Terror Financing
Nobitex is widely recognized as Iran's largest cryptocurrency exchange, a critical position within a nation heavily impacted by international sanctions. Its scale of operations is substantial, having processed over $8 billion in Iranian transactions since 2018, with significant flows to other major exchanges like Binance. As Iran faces severe international sanctions that largely isolate its traditional financial institutions from the global system, domestic crypto exchanges like Nobitex become vital conduits for accessing and moving funds. This applies to both legitimate financial activities for citizens and illicit operations for the regime. This position elevates Nobitex beyond a mere private company; its size and reach render it indispensable for the Iranian regime's efforts to circumvent sanctions and maintain a degree of economic activity. This elevated strategic importance inherently made it a prime target for a state-linked cyberattack, as its disruption directly impacts Iran's economic resilience under sustained international pressure.
Nobitex has been explicitly accused of being a "favorite sanctions violation tool" for the Iranian regime. Evidence suggests that the exchange does not merely passively allow sanctions evasion but actively facilitates it. It "doesn't even pretend to abide by sanctions. In fact, it publicly instructs users on how to use its infrastructure to bypass sanctions". A Reuters investigation further corroborated this, revealing that Nobitex offered direct guidance on "skirting sanctions right on its website". Moreover, Nobitex advises its customers to avoid direct crypto transfers, recommending "indirect flows" to "maintain security," a practice that inherently helps obfuscate the origins and destinations of funds. This public instruction on bypassing sanctions indicates a deliberate, institutionalized approach to circumventing international financial regulations, rather than passive involvement or individual user actions. This systematic approach poses a significant challenge to the effectiveness of international sanctions regimes. It demonstrates that sanctioned entities are actively developing and promoting sophisticated methods to undermine financial controls, leveraging the decentralized nature of cryptocurrency. This necessitates a proactive and adaptive response from sanctions authorities, potentially requiring more aggressive targeting of the technological infrastructure and key facilitators that enable such institutionalized evasion.
Allegations linking Nobitex to the financing of terror and the Iranian regime's illicit activities are substantial. Gonjeshke Darande explicitly stated that Nobitex is "at the heart of the regime's efforts to finance terror worldwide". Further corroboration comes from Chainalysis research in 2022, which indicated that a majority of Bitcoin extorted from ransomware victims by Iranian nationals linked to the Islamic Revolutionary Guard Corps (IRGC) was subsequently sent to Nobitex. These ransomware attacks specifically targeted U.S. critical infrastructure, including healthcare providers and schools. Additionally, OFAC designations have targeted individuals associated with Iran's IRGC for their involvement in ransomware and cybercrime, with some using cryptocurrency addresses that funnel funds directly to Nobitex. While not directly linking Nobitex to oil smuggling, it is established that Iran's regime relies heavily on revenue from oil sales to fund its destabilizing activities and support terrorist partners and proxies, utilizing complex money laundering networks to access international markets. This evidence reveals a clear nexus: IRGC-linked cybercriminals conduct ransomware attacks, funnel the illicit proceeds to Nobitex, and Nobitex is simultaneously accused of facilitating terror financing and sanctions evasion for the regime. This demonstrates a sophisticated ecosystem where cybercrime directly contributes to state-sponsored illicit finance. Nobitex appears to function as a critical financial off-ramp for funds generated through cybercriminal activities that are linked to the Iranian state, effectively laundering illicit proceeds for geopolitical objectives. This convergence makes financial intelligence and cybersecurity intelligence inextricably linked in countering state-sponsored threats, requiring integrated strategies to disrupt these complex financial pipelines.
A particularly striking claim made by Gonjeshke Darande is that "working at Nobitex is considered valid military service" under Iranian law. The group further asserted that this implies the exchange is "part of the country's defense and intelligence infrastructure" and "vital to the regime's efforts". If this claim is accurate, it fundamentally redefines how a cryptocurrency exchange is perceived within a state's national security framework. It would mean that the Iranian state formally recognizes its ability to conduct financial transactions and evade sanctions through crypto as directly contributing to its military and strategic objectives, akin to traditional defense or critical infrastructure sectors. This legitimizes attacks on such entities as acts against state military infrastructure, further blurring the lines between cyber warfare, economic warfare, and conventional conflict, and providing a strong justification for targeting by adversaries.
Table 2: Nobitex's Alleged Illicit Activities and Regime Links
| Allegation/Activity | Evidence/Source | Implications for Iranian Regime/International Community |
|---|---|---|
| Sanctions Evasion Tool | Gonjeshke Darande claims Nobitex is "favorite sanctions violation tool". Reuters investigation: Nobitex offered guidance on "skirting sanctions". Nobitex advises "indirect flows" to obfuscate origins. | Undermines international sanctions effectiveness; provides critical financial lifeline to sanctioned regime. |
| Public Instruction for Sanctions Bypass | Nobitex "publicly instructs users on how to use its infrastructure to bypass sanctions". | Indicates institutionalized, deliberate circumvention; challenges enforcement requiring adaptive responses. |
| Terror Financing Facilitation | Gonjeshke Darande: Nobitex is "at the heart of the regime's efforts to finance terror worldwide". | Directly supports state-sponsored terrorism and proxy networks; increases global security risks. |
| Recipient of Ransomware Funds | Chainalysis: Majority of Bitcoin extorted by IRGC-linked Iranian nationals from U.S. critical infrastructure (healthcare, schools) was sent to Nobitex. | Connects cybercrime to state-sponsored illicit finance; Nobitex acts as a money laundering conduit. |
| Employment as Military Service | Gonjeshke Darande: "working at Nobitex is considered valid military service". | Designates Nobitex as part of Iran's defense/intelligence infrastructure; legitimizes targeting as military action. |
| Large Volume of Iranian Transactions | Processed over $8 billion in Iranian transactions since 2018, significant flows to Binance. | Vital for Iran's economy under sanctions; central to regime's ability to access and move funds. |
VI. Iran's Illicit Finance and Cyber Landscape
The Iranian regime's reliance on cryptocurrency for bypassing international sanctions and funding its proxies has become increasingly pronounced. Sanctioned entities, including Iran's largest cryptocurrency exchange, Nobitex, accounted for a significant share of illicit crypto volume in 2024, although overall volumes reportedly decreased from 2023 levels. Cryptocurrencies provide distinct advantages for illicit actors, offering "ease of transactions, increased speed and anonymity, and a lack of regulation," making them a "dangerous tool that can circumvent financial sanctions". In 2022, the volume of illicit crypto transactions globally surpassed $20 billion, with a substantial 44% of those funds originating from activities associated with sanctioned entities. The U.S. Department of the Treasury's Financial Crimes Enforcement Network (FinCEN) has issued advisories specifically on identifying and reporting potential sanctions evasion related to Iran, noting the regime's reliance on oil sales to fund destabilizing activities and terrorist partners and proxies through complex money laundering networks. This dynamic situation illustrates an evolving, continuous struggle between sanctions enforcers and sanctioned regimes. Iran's reliance on crypto and its sophisticated illicit finance networks demonstrate an adaptive response to traditional sanctions. However, the reported decline in illicit crypto volume suggests that international efforts, including targeted designations by bodies like OFAC, may be having some impact. This highlights the continuous need for intelligence-driven, adaptive sanctions enforcement that anticipates and responds to evolving evasion tactics.
The Islamic Revolutionary Guard Corps (IRGC) plays a pervasive role in Iran's financial and cyber operations. Designated as a terrorist organization by the U.S., the IRGC is a principal branch of Iran's armed forces and has "metastasized into one of the most dominant political, security, economic, and ideological actors in Iran". Beyond its military functions, the IRGC is responsible for controlling Iran's missile and drone arsenals and managing support for the "Axis of Resistance". Critically, IRGC-linked individuals and entities have been sanctioned for their involvement in ransomware and cybercrime, with extorted funds demonstrably flowing to Nobitex. The U.S. has also identified Iran's construction sector as being directly or indirectly controlled by the IRGC, which is accused of building "terror and chaos". The IRGC's deep embedding in Iran's economy, intelligence, and cyber operations, combined with its traditional military roles, state-sponsored cybercrime, illicit finance, and control over strategic sectors, demonstrates that it functions as a sophisticated hybrid threat actor. Its pervasive influence allows it to leverage diverse tools—from missile arsenals to ransomware and crypto exchanges—to advance the regime's objectives. Countering such an entity requires a multi-faceted approach that integrates military, financial, and cyber counter-measures, recognizing the interconnectedness of its various illicit activities. In a sign of intensifying paranoia, the IRGC's Cybersecurity Command has even ordered officials and their security teams to avoid all internet-connected devices, including phones, smartwatches, and laptops. Furthermore, nine Iranian nationals were charged for conducting a massive cyber theft campaign on behalf of the IRGC, targeting universities, companies, and government agencies globally.
The broader context of U.S. and international sanctions regimes, administered by bodies like OFAC and the Financial Action Task Force (FATF), faces significant challenges in the realm of cryptocurrency enforcement. OFAC administers U.S. sanctions to disrupt terrorism financing and restrict financial transactions that threaten U.S. security. It has issued designations targeting individuals and entities, including cryptocurrency exchanges, facilitating illicit activities, which have shown to cause significant drops in inflows post-designation. The FATF develops global anti-money laundering (AML) and counter-terrorist financing (CFT) standards, including targeted financial sanctions related to terrorism and terrorist financing. Despite these efforts, the decentralized and often unregulated nature of cryptocurrencies continues to be exploited for sanctions evasion. A major challenge lies in enforcing regulations against exchanges that do not operate on U.S. soil, such as Binance (which processed billions in Iranian transactions) or Garantex. Regulators also face difficulties in tracking illicit funds due to the ease with which digital wallet addresses can be changed and the prevalence of "indirect flows" designed to obfuscate fund origins. One proposed solution to address these challenges is the introduction of personal criminal liability for the owners of exchange platforms that knowingly facilitate sanctions evasion. These challenges highlight a fundamental "regulatory lag," where existing legal frameworks struggle to keep pace with rapid technological advancements in the crypto space. Effective enforcement requires not just national sanctions but also a more robust and coordinated international approach to crypto governance, including harmonized Know-Your-Customer (KYC) and Anti-Money Laundering (AML) standards, enhanced cross-border data sharing, and potentially, mechanisms for imposing secondary sanctions or criminal liability on foreign entities and individuals that knowingly facilitate illicit crypto activities.
The Iranian government's response to cyberattacks and its own offensive cyber capabilities demonstrate a dynamic and evolving digital posture. Iran has been the target of a series of cyberattacks on its critical infrastructure, including gas stations, railway systems, and various industries. In response, the Iranian regime is reportedly preparing to regulate its crypto economy for increased transparency, and the Central Bank of Iran has taken steps to close access to the portals of cryptocurrency exchanges. These actions suggest an internal effort to either control and legitimize cryptocurrency use or to mitigate further exploitation. Concurrently, Iran possesses its own offensive cyber capabilities, as evidenced by a "largely unsuccessful" attempt by Iran and Hezbollah to hack an Israeli hospital. The U.S. is actively offering rewards for information on Iranian hackers, including those linked to the IRGC Cyber-Electronic Command, who are known to target critical infrastructure with malware like IOCONTROL. Analysts anticipate that Iranian cyber threat actors will likely "rededicate themselves" to attacks on Israel and potentially U.S. critical infrastructure in light of the escalating military conflict. This dual role, as both a target and a perpetrator in cyber warfare, illustrates a mature, albeit asymmetric, cyber conflict where both sides actively deploy offensive capabilities. The Iranian regime's efforts to regulate crypto internally could be a defensive measure to prevent further exploitation or an attempt to centralize control over a vital financial channel. The expectation of increased Iranian cyber activity against Israel and the U.S. signifies a predictable escalation pattern, underscoring the need for enhanced cyber defenses and intelligence sharing among potential targets.
Table 3: Examples of Sanctioned Entities/Addresses Related to Iranian Illicit Crypto
| Entity/Address | Type | Alleged Illicit Activity | Sanctioning Authority | Impact of Sanction (if available) |
|---|---|---|---|---|
| Nobitex | Cryptocurrency Exchange | Sanctions evasion, terror financing, receiving ransomware funds from IRGC-linked actors | Not directly sanctioned by OFAC in provided snippets, but targeted by cyberattack for these reasons | \~$48M USDT loss, website/app offline, threat of data release 1 |
| Garantex | Russian Cryptocurrency Exchange | Facilitating illicit crypto volume for sanctioned entities/jurisdictions | OFAC | Inflows dropped significantly post-designation 13 |
| NetEx24 | Centralized Exchange | Facilitating millions in transactions for illicit and sanctioned actors | OFAC | Inflows dropped significantly post-designation 13 |
| Bitpapa | Peer-to-peer Exchange | Facilitating millions in transactions for illicit and sanctioned actors | OFAC | Inflows dropped significantly post-designation 13 |
| Cryptex | Centralized Exchange | Facilitating millions in transactions for illicit and sanctioned actors | OFAC | Inflows dropped significantly post-designation 13 |
| GazaNow & Mustafa Ayash | Entity & Founder (Gaza-based) | Raising funds for Hamas | OFAC | Designated 13 |
| Tawfiq Muhammad Sa'id al-Law | Hawala Operator (Lebanon-based Syrian) | Providing Hezbollah with digital wallets for IRGC-QF funds | OFAC | Designated 13 |
| Ahmad Khatibi Aghada | Iranian National (IRGC-linked) | Ransomware, cybercrime, funds to Nobitex | OFAC | Designated, crypto addresses included as identifiers 15 |
| Amir Hossein Nikaeen Ravari | Iranian National (IRGC-linked) | Ransomware, cybercrime, funds to Nobitex | OFAC | Designated, crypto addresses included as identifiers 15 |
| Various Bitcoin Addresses (e.g., 1H939dom7i4WDLCKyGbXUp3fs9CSTNRzgL) | Cryptocurrency Wallet Addresses | Receiving extorted funds from ransomware victims (IRGC-linked) | OFAC | Designated 15 |
VII. Geopolitical Implications and Future Outlook
The cyberattack on Nobitex carries significant geopolitical implications, particularly for Iran's financial system and its ongoing efforts to circumvent international sanctions. The reported loss of over $48 million and the explicit threat to release sensitive internal data could severely disrupt Nobitex's operations and erode user trust, thereby significantly limiting its effectiveness as a tool for sanctions evasion. This incident may compel the Iranian regime to further centralize or exert greater control over its cryptocurrency economy, aligning with earlier reports of regulatory preparations and actions by the Central Bank of Iran to restrict access to crypto exchange portals. This attack, especially when viewed alongside the preceding assault on Bank Sepah and other critical infrastructure, signifies an intensification of economic pressure exerted through cyber means. This strategy aims to exacerbate Iran's economic vulnerabilities, particularly its ability to access foreign currency and fund its regional proxies under sanctions. By making crypto-based sanctions evasion riskier and more difficult, the attack contributes to a broader campaign of economic strangulation, potentially leading to increased internal economic hardship and pressure on the regime to alter its behavior.
The Nobitex and Bank Sepah attacks, occurring in rapid succession, demonstrate a heightened level of coordination and strategic targeting by Gonjeshke Darande, unequivocally signaling an escalation in the Israel-Iran cyber conflict. This conflict is increasingly characterized by the coordinated deployment of both kinetic military strikes and cyber operations. Cyber warfare, in this context, functions as a powerful force multiplier, allowing states to achieve strategic objectives and inflict costs without engaging in direct military confrontation. However, the persistent nature of these operations and their potential for significant disruption can lead to unintended escalation. The inherent ambiguity of attribution in cyber operations, while providing deniability, also complicates traditional de-escalation mechanisms and makes it harder to establish clear red lines. This increases the risk of miscalculation in the broader Israel-Iran conflict, where digital actions can have tangible, destabilizing effects.
In light of these developments, several recommendations for international stakeholders are critical regarding sanctions enforcement, cybersecurity, and counter-terror financing in the crypto domain:
- Enhanced Intelligence Sharing and Collaboration: There is an urgent need to foster greater collaboration among financial intelligence units (FIUs), cybersecurity agencies, and law enforcement entities globally. This collaboration is essential for effectively tracking illicit crypto flows and identifying state-sponsored cyber actors who exploit digital assets.
- Adaptive Sanctions Regimes: International bodies and national governments must develop more agile and technologically informed sanctions mechanisms. These mechanisms should be capable of rapidly identifying and designating new cryptocurrency addresses, exchanges, and obfuscation techniques employed by sanctioned entities to evade controls.
- Legal and Regulatory Harmonization: Advocating for robust international standards and legal frameworks is paramount to address the jurisdictional challenges inherent in regulating and enforcing against foreign crypto exchanges involved in illicit finance. This could potentially include mechanisms for imposing personal criminal liability on individuals who knowingly facilitate such activities.
- Capacity Building for Counter-Crypto Illicit Finance: Significant investment is required in training and developing specialized tools for financial institutions and regulators. This will enhance their capability to detect, analyze, and report suspicious crypto transactions, particularly those linked to state-sponsored activities and terror financing.
- Public-Private Partnerships: Encouraging greater cooperation between governments and the cryptocurrency industry is crucial. Such partnerships can lead to enhanced security measures, the implementation of more robust KYC/AML protocols, and improved sharing of threat intelligence to mitigate the abuse of crypto platforms for illicit purposes.
The complexity of the Nobitex incident, involving a state-sponsored cyberattack, illicit finance, sanctions evasion, and broader geopolitical conflict, underscores a fundamental truth: these intertwined threats cannot be effectively addressed by any single entity or discipline. This highlights the critical need for a holistic, multi-stakeholder approach that integrates cybersecurity, financial intelligence, law enforcement, and diplomatic efforts. International cooperation, shared best practices, and a unified front are essential to disrupt these sophisticated networks and mitigate the escalating risks posed by state-sponsored illicit finance and cyber warfare in the digital asset space.



 source:
source: 
